Universal Resolver
Resolve many different types of DIDs using a common interface
See Universal Resolver Docs
Appearance
For Decentralized Identity Developers & Solution Providers
This page gives a high-level overview of what Godiddy is and how it works.
If you want to get started with a practical introduction and learn about the Godiddy Client API, head over to the API Reference documentation.
Godiddy.com is a hosted platform that makes it easy for Decentralized Identity developers and solution providers to work with DIDs.
Godiddy makes it possible to:
across multiple DID methods and networks. Advanced functions include:
See the Quickstart or the individual API component pages for more information:
Godiddy.com is a platform that caters to a wide range of users who are interested in SSI and DID technology. Some of the users who use godiddy are:
Godiddy.com can be accessed either via a web frontend, or an API.
Also see the API Reference.
Our mission is to make it easy for Decentralized Identity developers and solution providers to work with DIDs across different methods and networks. We want to enable users to create, manage, and resolve DIDs using a single API that supports multiple DID methods, such as cheqd, ebsi, ethr, indy, and ion. We also provide users with a dashboard where they can get statistical insights into various aspects of DID operations, such as the number of transactions, errors, and networks.
We believe that DIDs are the future of digital identity and that they can empower users to have more control and ownership over their identity and credentials. We aim to provide a reliable and secure platform that supports the interoperability and compatibility of DIDs with different Decentralized Identity frameworks and standards.
Godiddy's services extend beyond mere digital platforms. We are actively shaping the real-world applications of decentralized identities. From enhancing privacy and security in online transactions to fostering a more transparent and accountable environment in various sectors, Godiddy's capabilities are instrumental.
For more information on Service Endpoints and Digital Product Passports click here.
Godiddy can be used in the real world to enable Digital Product Passport for physical products. A Digital Product Passport is a document that contains information about a product’s origin, history, and quality. It can be used to verify the authenticity of a product and provide transparency about its supply chain.
With godiddy, Decentralized Identity developers and solution providers can create DIDs for physical products and use them as an indirection layer for endpoints or links pointing towards information about the product. This information can be stored in a digital product passport that is accessible through a service endpoint specified in the DID document.
For more information visit our Medium page
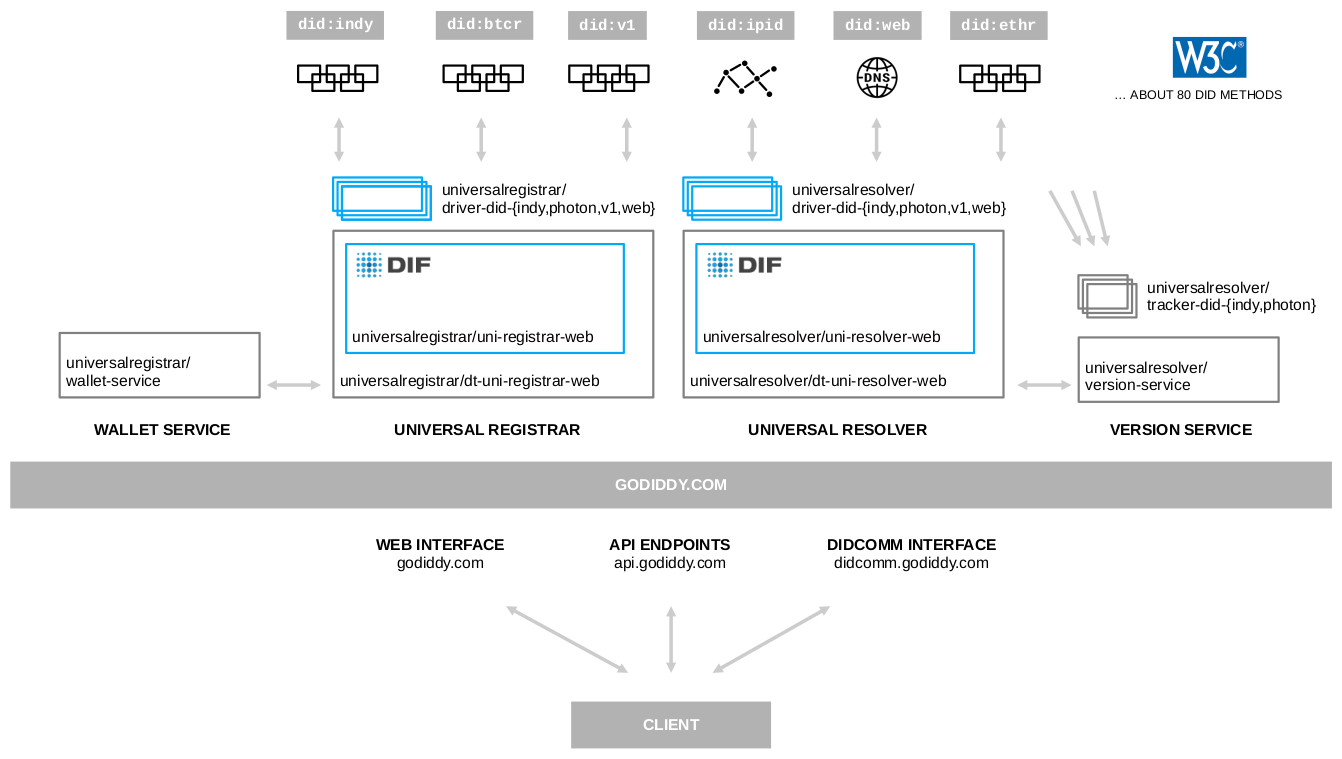
The following diagram outlines the major components of Godiddy.com:

Godiddy.com is provided by Danube Tech. Please write to us at contact@danubetech.com for more information.

Built using the well-known open-source tools Universal Resolver and Universal Registrar open source projects at the Decentralized Identity Foundation.